Frequently Asked Questions
This FAQ documents version 6.8 of the settings. Make sure to always upgrade to the latest version of the browser. If your question is not answered here, you can try to get answers in our Matrix room, or on r/LibreWolf and c/LibreWolf.
Alternatively, you could check the parts in the Firefox documentation that could be relevant:
- Protect your privacy.
- Manage preferences and add-ons.
- Helping with crashes.
- Error Messages
- Boost LibreWolf
General questions
I have a problem. Where do I open a new issue?
Once you have read the contribution guidelines and you are sure you want to open a new issue you can head over to our issue tracker on Codeberg.
Will you provide an Android version of LibreWolf?
At the moment nobody is working on it, and it is not something we have considered investing time in. We recommend using IronFox as an alternative.
Why don't you accept donations?
We don't want to deal with the administration required to properly handle donations. If we don't need funding, we won't risk becoming dependent on it. And also: no donations means no expectations. This means that people working on LibreWolf are free to move on to other projects whenever they want.
Will you change the default search engine?
We are going to keep DuckDuckGo since we believe it is a competent and privacy respecting search engine.
Users that have ethical problems with DDG can always change their default search engine with one click.
Do you have any contribution guidelines?
Before opening a new issue we require that you read the FAQ in full and that you check out the settings page. We also ask you to look for existing issues that address your problem, before opening redundant ones. Finally, we also appreciate when users try to reproduce their issues in a new profile to make sure their extensions and settings are not the root cause of the issue.
When opening a new issue make sure you follow the template if it exists, and after you did we ask you to contribute to it, by providing the needed details. When these simple rules are not respected, issues might be closed by maintainers.
Suggestions, improvements and contributions to LibreWolf are appreciated in the form of merge requests, or alternatively well documented issues. We suggest interested contributors to join us on Matrix.
In my country I can't download uBO from Mozilla's store. What can I do?
If you can, we recommend downloading from the GitHub releases page. In any case, do NOT download extensions from random websites.
More details are available at this link.
Security and Privacy:
How often do you update LibreWolf?
LibreWolf is always based on the latest version of Firefox. Updates usually come within three days from each upstream stable release, at times even the same day. Unless problems arise, we always try to release often and in a timely manner.
It should however be noted that LibreWolf does not have auto-update capabilities, and therefore it relies on package managers or users to apply them.
Can I use LibreWolf with Tor?
Please don't.
The Tor network is designed to give you complete anonymity, but it can be compromised if you use it with any browser other than the Tor Browser. If you want anonymity, download the Tor Browser.
The Tor Browser is specifically designed to reduce fingerprintability and to work on Tor. Using LibreWolf or any other browser would make you stand out and it is not recommended.
DoH: What's the stance on DoH?
LibreWolf disables DoH by default. During the v130.0-1 and v130.0-3 releases, LibreWolf may have changed your DoH settings. Please check them.
DoH is "DNS over HTTPS", an alternative protocol for looking up domain names over a secure web connection. More information about the protocol on Wikipedia.
Looking at the problems of having one cloud entity being able to log all your DNS traffic, this is the major breaking point. On the other hand, DoH does provide security against insecure networks logging your DNS traffic.
This is a trade-off that the browser can't really make for the user. So we turn it off by default. Doing so does not prevent us from providing reasonable generic values for DoH, for when the user wants to enable it.
DoH: How do I disable DoH?
Go to the menu, and in: Settings >> Privacy & Security >> 'Enable DoH using' and select: 'Off'.
Or, in your librewolf.overrides.cfg (or about:config), put the following
setting:
pref("network.trr.mode", 5);DoH: What is the currently recommended way to enable DoH?
Go to the menu, and in: Settings >> Privacy & Security >> 'Enable DoH using' and select: 'Increased protection'. The settings given in the snippet below should be set as default already.
Please note the DoH server used before you enable DoH. Note the jurisdiction of this server. If you're fully confident, you could try the DoH setting 'Max Protection'.
If you really want to lock down DoH for yourself, you can put the following
settings in your librewolf.overrides.cfg (or about:config):
pref("network.trr.mode", 2);
pref("network.trr.uri", "https://dns10.quad9.net/dns-query"); // Current 'reasonable default': No Filering
// Additions by Acideburn in https://codeberg.org/librewolf/issues/issues/1975#issuecomment-2301916 , and other PR's
pref("network.trr.default_provider_uri", "https://doh.dns4all.eu/dns-query"); // Define a fallback DoH server (used only in mode 1)
pref("network.trr.strict_native_fallback", false); // Allow native fallback
pref("network.trr.retry_on_recoverable_errors", true); // Retry on recoverable errors
pref("network.trr.disable-heuristics", true); // Disables the canary telemetry detection request "use-application-dns.net" for DOH
pref("network.trr.allow-rfc1918", true); // Allows the use of private IP addresses (RFC 1918) in DOH responsesWhy do you disable Google Safe Browsing?
We disable Safe Browsing as we consider it a censorship concern, and we would rather not let Google control another aspect of the internet. With that being said, Safe Browsing is still a good security tool and Mozilla's implementation is privacy respecting: for this reason those who are interested in the extra security, and in particular less technical users, can and should safely enable it.
Despite the above concerns, we are open to re-evaluating and recommending Safe Browsing with the right defaults. Unfortunately, to be fully functional, Safe Browsing requires to include a developer key at build time: this means that a Google account becomes a hard requirement for anyone building from source. This also means that LibreWolf cannot provide a fully functional Safe Browsing experience at the moment.
More details are available at this link.
Do you recommend using any extensions?
Yes, in fact we include uBlockOrigin in the browser. We also have a few suggestions that you can look at.
However, as a general rule, you shouldn't install too many add-ons. Each add-on is a new potential source of security vulnerabilities and may make you stand out.
What are some tips on a more hardened setup?
To improve your privacy we suggest enabling letterboxing, in order to prevent your real window size from being fingerprinted. This can be especially useful if you resize your window.
It's also possible to further limit the behavior of cross-origin referers, although it's worth noting that this might cause breakage.
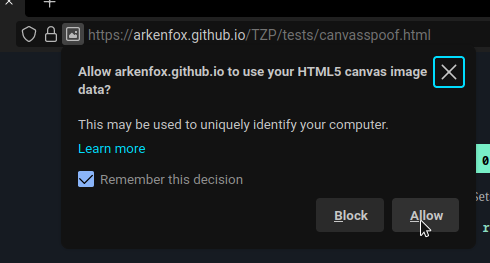
Should I allow canvas access? How do I do it?
Please be mindful when allowing canvas access as it is a very strong fingerprinting vector; however, if you are already logged into a website you shouldn't stress too much about giving it canvas access because they already know who you are.
Canvas can be handled on a per-site basis thanks to RFP. You will be prompted for access next to the URL bar, so look for the icon there.
![]()
Should I allow WebGL context creation?
WebGL (short for Web Graphics Library) is used for drawing hardware-accelerated 2D and 3D graphics, often used in games and for interactive applications such as maps. More information about WebGL on Wikipedia.
There has been work done to mitigate the fingerprinting vector of WebGL, but it is preferable to only allow it when a site actually requires it to function. Only enabling it per site instead of globally also reduces the attack surface of the browser and provides better security.
Generally, most sites will function without it, and it is recommended to only enable it when a site is broken without it.
Some sites that need WebGL would include:
- Google Earth
- Google Photos Editing
- HERE WeGo
Why is the built-in password manager disabled?
We believe you should use a password manager that is better for your security and comfort, please consider some of the options in our recommended addons.
Does LibreWolf use HTTPS-Only mode?
Yes, and you won't need any extension for that. HTTP can still be allowed for certain sites.
Does LibreWolf make any outgoing connections?
Yes, but they aren't in any way privacy invading and they were carefully evaluated. We consider these connections to be important for user security and to provide a safe browsing experience, as they fetch necessary updates to security features and blocking lists.
Specifically, LibreWolf makes connections to fetch and update data such as:
- CRLite: For certificate revocations, providing protection against compromised security certificates.
- Enhanced Tracking Protection (ETP): To update the tracker blocking lists, helping against tracking and fingerprinting.
- Public Suffix List: Used to properly determine boundaries between different domains to prevent cookies from being set across sites.
- uBlock Origin (uBO): To update its blocking lists that protect against ads, trackers, and malicious domains.
- GPU Blocklist: To update the list of broken or vulnerable graphics drivers via Remote Settings, which helps prevent browser crashes and security exploits.
- Local translation ML models: If you actively choose to download them, allowing you to perform privacy-respecting translations locally.
LibreWolf also maintains an open WebSocket towards Mozilla's push server to check whether you have received push notifications from websites you have subscribed to. This push service is also used to inform LibreWolf about any urgent updates to these security features and blocking lists. If you wish to disable push notification prompts, please see how to disable push notifications.
With that being said, LibreWolf is still committed to removing all privacy invading connections, and to keep all connections to the bare minimum required to maximize and balance privacy and security.
What is Enhanced Tracking Protection?
In LibreWolf we decided to enable Enhanced Tracking Protection, as it plays nicely with uBO and it can block some extra scripts. Additionally, when set to strict it includes dFPI, SmartBlock, enhanced cookie cleaning, stricter referer policies and URL query stripping. For this reason, we always suggest the default strict mode, and when using it please do not enable FPI, as it interferes with the more recent dFPI.
Finally, there's no point in changing from strict to any other mode, as strict mode doesn't usually cause any kind of breakage, and changing to custom mode to block cookies will come at the expense of disabling partitioning: not worth it, so we decided to hide the UI that allows users to change this setting. You can instead whitelist specific websites from the urlbar. More details are available at this link.
Tracking Protection requires some occasional outgoing connections, in order to fetch its blocking lists: these connections are harmless for privacy, and TP has a flawless track record in this regard. A particular important connection is the one that TP makes on first launch, as without it the feature cannot effectively work. If you want, you can block these outgoing connections by using the following overrides:
defaultPref("browser.safebrowsing.provider.mozilla.updateURL", "");
defaultPref("browser.safebrowsing.provider.mozilla.gethashURL", "");As stated above, and despite what you see in the Settings UI, blocking these connections will cause TP to stop working, as it won't be able to use the lists that allow it to block known tracking, cryptomining and fingerprinting scripts.
Why isn't First Party Isolate enabled by default?
FPI is not enabled by default as we use dFPI, and the two do not work well together. dFPI is a newer implementation and it causes less breakage, plus it is included by default when using Tracking Protection in strict mode.
Please also notice that dFPI makes containers and containers extensions redundant, unless you want to protect your privacy when visiting the same website multiple times, during the same browsing sessions.
Why can't I use always-on private browsing?
We have decided to hide that option as it doesn't provide any benefit over the default cleaning mechanism of LibreWolf. Instead it introduces many regressions, as it doesn't respect cookie exceptions and installed addons, while also being fingerprintable.
Can LibreWolf protect my public IP address?
No. If you care about protecting your IP address, you should use a VPN or even better use the Tor Browser.
How do I disable IPv6?
Instead of disabling IPv6 in the browser, we recommend enabling the IPv6 privacy extension at the OS level. macOS and Windows users are already covered, but some Linux distros do not enable it by default.
Does the bookmarks toolbar impact RFP's window size protection?
If you set its visibility to "Only show on New Tab", the bookmarks toolbar can alter inner window size slightly deviating from the rounded value: while you should not stress over this, we generally recommend to set the visibility to "Always Show" or "Never Show".
The current default is "Always show" in an effort to avoid messing up RFP's window size without being user hostile.
Should I disable accessibility services?
While we don't disable accessibility services by default, you might want to consider disabling them if you don't need them.
- It is not recommended to disable it, if the browser is being used with impairment assistive software.
- You can disable it if an anti-malware tool requires you to, without providing any other options.
- If you are using an educational or enterprise network, it is recommended that you contact your administrator about disabling accessibility services.
- If any other third-party software causes problems because of accessibility services, you can disable it if there is no other way.
To disable accessibility services, you can visit about:config and set the value of accessibility.force_disabled to 1.
How do I delete the browsing history on close?
Go to Settings > Privacy & Security > History. Check "Clear history when LibreWolf closes". You should also click the "Settings..." button next to it to select exactly what you want to be deleted.
Usability
What are the most common downsides of RFP (Resist Fingerprinting)?
It is possible that users will experience breakage because of RFP: usually this is caused by canvas access, which can be relaxed on a per-site basis.
Other common problems brought by RFP include:
- spoofed timezone.
- forced light theme.
- smaller and fixed window size on startup.
- suppressed keyboard modifier events using alt-keys.
These annoyances are intended to protect your privacy. Tweaking them using extensions or preferences significantly impacts the effectiveness of RFP, both for the users themselves, and the rest of the userbase: modifications create a subset of users who stand out and reduce the number of RFP users who look the same, making it worse for everyone.
For this very reason we suggest against modifying any metric involved in RFP, as even a single change could make it useless. We also suggest users to get used to RFP and stick with it as much as possible: it is a very powerful tool that gets improvements as the result of the Tor Uplift Project, and it will surely benefit your privacy in a major way.
In case you are really sure you would like to adjust these settings, you could
try switching to fingerprinting protection instead by first disabling RFP in the
LibreWolf settings, or
in your overrides and then
either setting overrides or about:config like this:
defaultPref("privacy.fingerprintingProtection", true);
defaultPref(
"privacy.fingerprintingProtection.overrides",
"+AllTargets,-CSSPrefersColorScheme"
);This would keep most of the fingerprinting protection active, while still letting websites know whether you prefer light or dark theme. The other available FPP override targets can be found here.
In case you aren't that concerned by fingerprinting and decide to disable both RFP and FPP, please consider using an extension like CanvasBlocker to retain at least a minimum amount of fingerprinting protection.
Why am I seeing striped images?
If you see striped images in your browser, that's most likely caused by the fact that the website needs canvas access to display them properly. Check out how to allow it.
What should I do if video conferencing is not working?
Videoconferencing platforms may require to enable WebGL and to allow autoplay.
Why is Session Restore not working?
Session restore will not work unless you preserve your browsing history. If you want to use session restore, make sure that you are not deleting history on close.
How do I stay logged into specific websites?
Add an exception at Settings > Privacy & Security > Cookies and Site Data >
Manage Exceptions. Make sure you add a website to the exceptions before you
login, both http and https versions of the domain. If you want to stay
logged into www.example.com enter example.com and click on "Allow": you
should then see the two versions listed, and you can go ahead and save the
changes.
Why is LibreWolf forcing light theme?
This is one of the privacy measure that come with RFP (Resist Fingerprinting). Our stance is that if you care about fingerprinting protection you should never alter RFP behavior in any way.
If you still want the dark theme for web content, check whether your favourite websites allow to set it manually.
Why does LibreWolf not remember my window size?
As mentioned in this FAQ this is part of RFP: the idea is to protect your actual window size by returning a rounded value.
How do I enable search suggestions?
If you use a privacy respecting search engine go to Settings > Search > Search Suggestions, and enable search suggestions.
How do I add a search engine?
LibreWolf provides a selection of privacy respecting search engines, but you can add more by following this guide.
Please note that some search engines, most notably Google, do not comply with the OpenSearch standard so you will not be able to add them the usual way. In that case, you can also check The Mycroft Project for an alternative source of search engine plugins.
How do I allow autoplay of media?
Autoplay can be controlled on a per-site basis from your urlbar.
How do I fully prevent autoplay?
The default autoplay strategy used in LibreWolf is called sticky and it's similar to the one found in other modern browsers. To avoid breakage it is not as strict as a full fledged user-triggered autoplay and it allows videos and thumbnails to play in some cases.
If you prefer a stricter autoplay policy you should have a look at this override recipe.
How do I enable push notifications?
Push notifications require to set a per-site exception, just like with cookies.
How do I disable push notifications?
If you are not interested in push notifications and want to disable the prompts asking for permission, you can do so from the settings:
- Open LibreWolf Settings (
about:preferences). - Click on Privacy & Security in the left sidebar.
- Scroll down to the Permissions section.
- Click the Notifications button.
- Check the box at the bottom that says "Block new requests asking to allow notifications".
- Click Save Changes.
Alternatively, you can change this via overrides or about:config by setting:
defaultPref("permissions.default.desktop-notification", 2);This changes the behavior from 0 (Always Ask) to 2 (Block). This blocks the
prompts from appearing, and without your explicit confirmation, no website can
send you push notifications.
Note: You should NOT disable dom.push.enabled. Doing so will break the
push security updates mentioned in the
outgoing connections FAQ.
How do I enable DRM?
We disable DRM by default, as we consider it a limitation to user freedom. Take a moment to read about it before you go ahead and enable it.
DRM support can be enabled from Settings > General > Digital Right Management (DRM) Content. Additionally, a pop-up and an icon in your URL bar will show up when a website is trying to use DRM.
Can I safely change language in the browser?
Yes, you can normally apply language packs from the settings. To protect your
privacy, LibreWolf will make you appear to websites as a en-US user.
Can I also change the language of the web content?
Yes, but you will need overrides since we enforce en-US.
This comment
offers some guidance, using German as an example.
Can I set a default download directory?
As a security measure, LibreWolf asks for user interaction after each download. You can change that in Settings > General > Files and Applications > Downloads > Save files to..
Can I use Firefox Sync with LibreWolf? Is it safe to do so?
Yes, you can enable it in your the LibreWolf specific UI or in your overrides. There aren't significant downsides as Firefox Sync encrypts your data locally before transmitting it to the server. Additionally, you can self-host the old version of the server if you really don't want to use Mozilla's, and there's work being done to have the new version equally easy to self-host. Find out more about the technical details of Sync's implementation here and here.
When using Sync across multiple installations you might want to disable settings synchronization to avoid unintentional changes.
I'm getting the "SSL_ERROR_UNSAFE_NEGOTIATION" error. What can I do?
The server you are trying to reach does not support
RFC 5746 and is potentially
vulnerable to MiTM attacks. You can bypass this warning by flipping
security.ssl.require_safe_negotiation to false in about:config, but we do not
recommend adding this to your overrides as it is a bad default.
I'm getting "SEC_ERROR_OCSP_SERVER_ERROR". What can I do?
We enable OCSP in hard-fail mode, meaning that if the revocation status of a certificate cannot be verified because the CA cannot be reached, then it will be treated as broken. While this improves security, it could also decreases usability as OCSP servers tend to be down often.
If you're experiencing this error:
- OCSP servers tend to get blocked by host files and blocking lists by mistake, so check your firewall and blocking lists first.
- OCSP is not compatible with most proxy and vpn extensions, so that's also something to consider.
If instead a server is actually down, you can consider disabling hard-fail mode in the LibreWolf settings, or using overrides.
I'm getting "MOZILLA_PKIX_ERROR_KEY_PINNING_FAILURE". What can I do?
We enable strict Public Key Pinning, so user level MiTM is not supported by default: this is problematic when an antivirus is trying to monitor your network traffic by using its own certificates.
If you use this kind of antivirus software and you want to disable this, you
need to change security.cert_pinning.enforcement_level to 1 in about:config.
How do I enable DNS-over-HTTPS?
You can use the dedicated UI in the settings of the browser, in the Privacy & Security category specifically. Just like in Firefox, you can choose between four different modes and select a provider of your choice.
By default DoH is not enabled in LibreWolf.
Linux specific questions:
Can't open links with LibreWolf when using Wayland
The solution is also described in this issue.
When setting LibreWolf as a handler to open links with, in some circumstances, environment variables parsed during "regular" launch are not parsed / applied when opening LibreWolf as a handler (XDG MIME handling) when using Wayland. LibreWolf then either gets launched without opening the link or by giving an error ('LibreWolf is already running').
This can be fixed by placing a modified .desktop file in
~/.local/share/applications/.
It's easiest to just copy the existing .desktop file (for native packages
/usr/share/applications/librewolf.desktop, for Flatpak
~/.local/share/flatpak/exports/share/applications/io.gitlab.librewolf-community.desktop)
to ~/.local/share/applications/ and edit the Exec lines:
Flatpak
# io.gitlab.librewolf-community.desktop
Exec=/usr/bin/flatpak run --env=GDK_BACKEND=wayland --branch=stable --arch=x86_64 --command=librewolf --file-forwarding io.gitlab.librewolf-community @@u %u @@
Exec=/usr/bin/flatpak run --env=GDK_BACKEND=wayland --branch=stable --arch=x86_64 --command=librewolf --file-forwarding io.gitlab.librewolf-community @@u %u @@
Exec=/usr/bin/flatpak run --env=GDK_BACKEND=wayland --branch=stable --arch=x86_64 --command=librewolf --file-forwarding io.gitlab.librewolf-community --private-window @@u %u @@
Exec=/usr/bin/flatpak run --env=GDK_BACKEND=wayland --branch=stable --arch=x86_64 --command=librewolf --file-forwarding io.gitlab.librewolf-community --ProfileManager @@u %u @@
For Flatpak, this might also be possible by using
flatpak override --user --env=GDK_BACKEND=wayland io.gitlab.librewolf-community,
but this is not yet tested.
Native Linux Package
# librewolf.desktop
Exec=env GDK_BACKEND=wayland MOZ_ENABLE_WAYLAND=1 /usr/lib/librewolf/librewolf %u
Exec=env GDK_BACKEND=wayland MOZ_ENABLE_WAYLAND=1 /usr/lib/librewolf/librewolf --new-window %u
Exec=env GDK_BACKEND=wayland MOZ_ENABLE_WAYLAND=1 /usr/lib/librewolf/librewolf --private-window %u
How do I get native messaging to work?
To get native messaging to work, for example for the Plasma Integration, create two symlinks by running these commands:
sudo ln -s /usr/lib64/mozilla/native-messaging-hosts /usr/lib/librewolf/native-messaging-hosts
How can I get Tridactyl's native messaging to work when I install LibreWolf with Flatpak?
To get Tridactyl's native feature to work Tridactyl's install script needs to look into LibreWolf's app data directory and be allowed to read the user's RC file.
Execute the following:
curl \
https://gitlab.com/librewolf-community/browser/common/-/raw/master/helpers/tridactyl-install.sh \
> /tmp/tridactyl-install.sh
sed -i \
's/\.librewolf/\.var\/app\/io\.gitlab\.librewolf-community\/\.librewolf/g' \
/tmp/tridactyl-install.sh
chmod +x /tmp/tridactyl-install.sh
/tmp/tridactyl-install.sh
# If installed onto the system, rather than the user, then remove `--user`
flatpak --user override io.gitlab.librewolf-community --filesystem="${XDG_CONFIG_HOME:-~/.config}"/tridactyl
flatpak --user override io.gitlab.librewolf-community --filesystem="${XDG_DATA_HOME:-~/.local/share}"/tridactylI installed LibreWolf and KeePassXC using Flatpak and it does not work
As you may have noticed when installing both LibreWolf and KeePassXC via Flatpak, they do not work together out of the box. We suggest reading this guide to fix this issue!
What are the Linux options for ARM64, or aarch64 architectures?
Support depends highly on the distribution you are using. The Flatpak version of LibreWolf is available for ARM, and generic binary ARM tarballs are also available.
Is "Importing GPG key 0x2B12EF16" ok?
If you followed the instructions at https://librewolf.net/installation/fedora to install LibreWolf on Fedora, you may receive the following prompt when trying to update your system:
Importing GPG key 0x2B12EF16:
Userid : "LibreWolf Maintainers <gpg@librewolf.net>"
Fingerprint: 662E 3CDD 6FE3 2900 2D0C A5BB 4033 9DD8 2B12 EF16
From : https://rpm.librewolf.net/pubkey.gpg
Is this ok [y/N]:
It is okay to accept this prompt, but make sure to check that the fingerprint
you get is 662E 3CDD 6FE3 2900 2D0C A5BB 4033 9DD8 2B12 EF16. The "From" field
may vary between rpm.librewolf.net and repo.librewolf.net, which does not
matter as they both serve the same repository.
How do I migrate to the new XDG paths?
There is no officially supported migration path currently, since there are still open issues.
Do this at your own risk
If you still want to migrate:
Back up your ~/.librewolf (you'll later need this to copy over your profiles and overrides).
Delete your ~/.librewolf (it must be removed because ~/.librewolf always takes precedence).
Then start LibreWolf so it creates the new paths.
If you use Firefox Sync, it should automatically sync your settings after you sign in. (You'll still need to manually move your overrides file if you have one.)
Otherwise:
Replace the contents of either XDG_CONFIG_HOME/librewolf/librewolf or, when XDG_CONFIG_HOME is not set, ~/.config/librewolf/librewolf with the contents of your backed-up ~/.librewolf.
You will need to reinstall your extensions
Click on the puzzle icon
![]()
Press the radio button for each extension to disable it
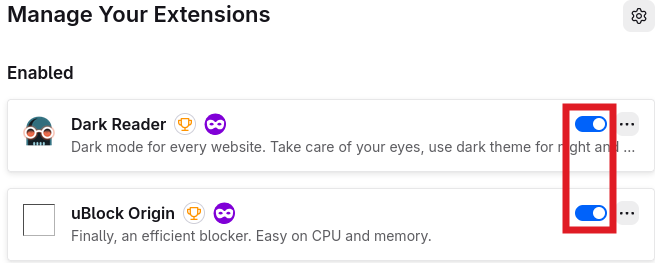
It should then look like this
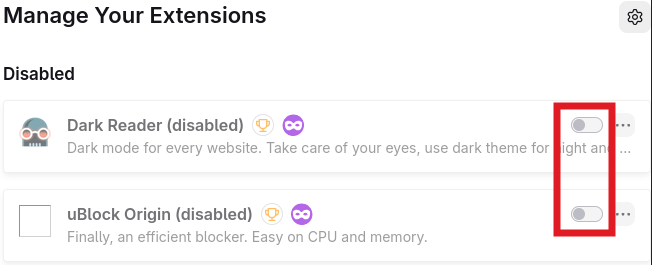 And then reanable them again
And then reanable them again
It should then look like this
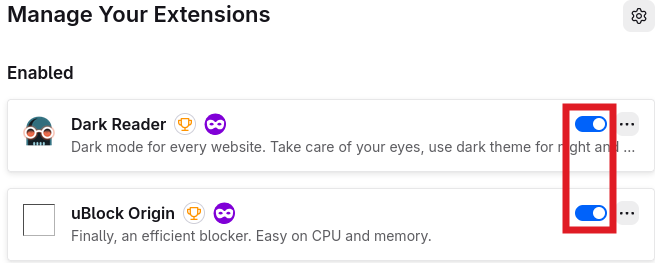
Restart LibreWolf and your extensions should now be working again
![]()
macOS specific questions:
How do I install LibreWolf on macOS?
You can either build from source, install using a disk image from the releases or install using Homebrew.
How do I build LibreWolf on macOS?
You can build LibreWolf from source by cross-compiling it on Linux. For more details head over to our source repo or to the bsys6 repo and read the documentation.
How do I update LibreWolf on macOS?
To update the browser on macOS you need to grab the latest .app and drag it into
your Applications directory, or if you installed using Homebrew you can do it
as you would for every other cask.
Is LibreWolf available via Homebrew?
LibreWolf is available as a cask, so you can install entering
brew install --cask librewolf.
Does LibreWolf work on Apple Silicon machines?
Yes, we provide native builds for both Intel and ARM based machines. If you own
an Apple Silicon powered MacBook the relative builds are referred to as
aarch64, they are cross-compiled and we did not test them before release.
Please consider that the build time on Apple Silicon is relatively low, so
building from source is probably worth it in any case.
Why is LibreWolf marked as broken?
It is possible that Apple Silicon users see their recently downloaded LibreWolf flagged as broken or unsafe by the OS.
This happens because we do not notarize the macOS version of the browser: we don't have a paid Apple Developer license and we don't want to support this signing mechanism that is put behind a paywall without providing significant gains.
You can remove the quarantine attribute from the Application using this command:
xattr -dr com.apple.quarantine /Applications/LibreWolf.app
How do I get native messaging to work?
You need to add the following symbolic link:
ln -s ~/Library/Application\ Support/Mozilla/NativeMessagingHosts ~/Library/Application\ Support/LibreWolf/NativeMessagingHosts
This is necessary to get KeePassXC-Browser extension to work, and for biometric authentication in the Bitwarden extension.
Windows specific questions
Who is OSSign (Scheibling Consulting AB)?
We rely on OSSign, which is a project aiming to provide free code signatures for open source projects, to sign our binaries on Windows.
This may lead to the Windows UAC prompt showing "This software has been signed by OSSign", with the verified publisher being "OSSign (Scheibling Consulting AB)" from Uppsala (SE). That is to be expected, and does not mean that LibreWolf is affiliated with OSSign (Scheibling Consulting AB) in any capacity other than the code signing.
I have Kasperky antivirus. Why does my New Tab page not work?
This is a known issue with Kasperky: windows#313, windows#303. Please exclude LibreWolf from Kaspersky's monitoring, and it should go back to normal.
How do I set up Bitwarden's biometric authentication?
This is an ongoing issue where we can only help you with a workaround:
Open the Registry Editor and go to
Computer\HKEY_CURRENT_USER\SOFTWARE\Mozilla\NativeMessagingHosts\ and/or
HKEY_LOCAL_MACHINE\SOFTWARE\Mozilla\NativeMessagingHosts. Create a new key
called com.8bit.bitwarden in the left-side panel of RegEdit (or your registry
editor of choice, fellow home users). Set the Default REG_SZ to contain the
path to Bitwarden Firefox's Native Messaging Manifest:
...\browsers\firefox.json. The path may look something like this, your mileage
will wary:
C:\Users\milk\scoop\apps\bitwarden\current\bitwarden-appdata\browsers\firefox.json.
Once you've done that, you should be able to setup the Native Messaging bridge between LibreWolf and Bitwarden for biometric authentication.